Best practices to prevent phishing attacks
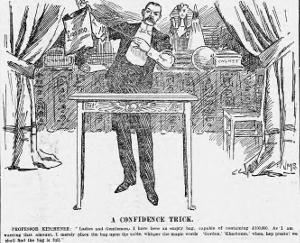
“Phishing” is the modern version of the ”Confidence trick” used by Samuel Thompson in the 19th century although these kind of tricks were already known since the middle ages. This trick exploits very common human characteristics like dishonesty, vanity, compassion, credulity, irresponsibility, naïveté and greed.
Phishing email messages try to deceive users by appearing to come from a reliable source to get the users’ private information. That information is used in identity theft, to steal funds from bank accounts, to infiltrate in a network to wreak havoc, etc.
Victims are deceived by modifying some header fields and the contents of the message to imitate an email from a reliable source.
The Phishing message is trying to get names, passwords, credit card numbers, bank accounts, etc. On other occasions it’s trying to infect the computer with a backdoor virus used in industrial espionage or intellectual property theft.
There are several phishing scams. Some of them are :
-
Generic phishing : A generic message that appears to come from a trusted source and it’s sent to a large number of email accounts hoping some of them will take the bait.
-
Spear phishing : It’s a personalized email message trying to deceive one person. It includes some personal information about the victim and it appears to come from someone known to the victim to gain his/her trust.
-
Whaling : This is spear phishing made to high level executives from big corporations. It’s used in corporate espionage.
Many email service providers have spam, phishing and malware filters installed but they’re not 100% safe.
Those filters search for signs of spam by analyzing the text, addresses and attached files. If the number of signs of spam in a message exceeds certain threshold, it’s marked as spam or discarded.
These filters are always one step behind the creators of phishing messages. For this reason, users must have some basic notions to identify the threats that reached the mailboxes.
Internet addresses
Before describing phishing messages you should understand some basic concepts about Internet addresses.

An Internet address can be represented as a series of numbers separated by dots and they’re called “IP addresses”, for example “127.0.0.1”.
Other addresses are made of words separated by dots and they’re called “Internet domains”, for example “example.com”.
Each domain correspond to an IP address but domains addresses are much easier to remember.
You can add words to the left of the domains separating them with dots to form subdomains, for example "mail.example.com" or "www.example.com". With those subdomains you can identify different services like an email server and a web server that belong to the example.com domain.
The last word to the right in the last example (“com”) is only used to group domains by their activity, country, etc. but they can have different owner.
To use an Internet address in a web browser you add “http://” or “https://” to the left. For example, https://www.example.com
In email clients you add a user name to the left of the domain address, separating them by a “@” sign to get an email address. For example, user@example.com
Criminals try to deceive users by using these tricks to make them believe the addresses they click are trustworthy :
-
Adding the name of a trusted company as subdomain of another address. For example, www.microsoft.example.com looks like it belongs to Microsoft but in fact it’s a subdomain of example.com. Another example, http://signin.ebay.com@120.32.56.98/ belongs to the IP address 120.32.56.98 and it has absolutely nothing to do with eBay.
-
By using domains with a very similar name. They can add small changes that can go unnoticed if your read it too fast, like swapping a letter for a number. For example, goog1e.com has a “one” instead of an L.
-
Use IP addresses so the user can’t recognize the domain they belong to.
Generic phishing characteristics
This type of phishing sends an unsolicited email message to many people and it usually appears to come from a well known company or organization to gain the victim’s trust.
The message header usually has :
-
The ‘From’ address doesn’t belong to the domain of the company that the message is trying to impersonate. On some occasions, fraudsters use free email service providers. Sometimes these addresses have random characters and numbers, like name_k3z9f@example.com
-
Multiple ‘To’ addresses.
-
‘Reply-to’ address different than the ‘From’ address, even from another domain.
-
The message was sent to an address that wasn’t provided to the company that supposedly sent it.

The message body usually has :
-
A very similar appearance to other legitimate messages sent by said company. The fraudsters use the original logos and images.
-
Some of the links use addresses from a different domain than the domain of the company they try to impersonate. Sometimes the real link address is hidden and the text shown in the link is deceiving. It’s necessary to move the mouse cursor over the link to show the real address.
-
They use a generic greeting like “Dear Sir/Madam” instead of the personalized greeting because there are many recipients.
-
Grammatical errors, typos and automatic translations.
-
On some occasions there are no details of the company in the message footer or they are vague.
-
To bypass some filters the messages may have these characteristics :
- The email message consists of a single image which includes the fraudulent text.
- The email message consists of a single link to a malicious website.
- Some words are misspelled so computers don’t recognize them but human beings do. For example, “vi@gr@” instead of “viagra”.
The message text :
-
It’s usually something that it’s too good to be true.
-
It asks the victim to provide private information in a form found inside the message or in a malicious web page. In this case, they add a link or a button to visit that web page.
-
It could even ask for money directly.
-
These frauds may use some of the marketing persuasion techniques :
- Urgency : The victim will be more prone to take impulsive decisions and skip security checks. It’s usually followed by threats, deadlines or product scarcity.
- Herd behavior : The victim will probably do everything in his/her hand to be socially accepted if he/she reads messages like “Everybody is doing it, and you?”.
- Authority : Sometimes these messages include the names of respected brands or companies. The victims know them very well and they will be inclined to believe them because they consider them an authority in their fields.
- Reciprocation : The readers of the message will be prone to follow the indications if they received a gift or a favor.
- Exclusivity : The message makes the reader believe that he/she belongs to a reduced group of people selected to try a product. Sometimes the fraudsters also make them believe that this is confidential information and only they know it.
- Appeal to feelings : The message makes the victim believe he/she is going to donate some money to those in need.
- Curiosity : The fraudsters may offer a supposed way to know what others think about the victim.

Some examples used in generic phishing messages :
-
Lottery or raffle prizes in which the victim didn’t participate. They ask to pay a fee to receive the prize.
-
Bank messages with debt threats, asking to validate the credit card information or asking to click on a link and log in with your bank account password.
-
Messages from government agencies asking for private data.
-
Messages from a known software company with a warning about a possible problem in the victim's computer. They ask for money to fix it.
-
Messages asking for a reward because they say they have your bank account.
-
Investment offers with guaranteed results or spectacular revenues that need an initial payment or they ask for some personal information.
-
Job offer that needs an initial payment to be selected. Usually they offer a big salary with little effort.
-
A nigerian dictator needs to get out of his country and he also needs an honest citizen that provides his/her bank account to transfer his money. That person would receive a huge sum of money for transferring the funds but to prove his/her worthiness, the citizen must previously transfer some amount of money to the dictator’s bank account.
-
Scholarships or grants that ask for an initial payment to be selected.
-
Legal threats, unpaid debts, account closure or cancellation, etc. They usually ask for money, to call a high rate phone number or to visit a malicious website to check the account status.
-
Message saying that the reader is the only beneficiary of an inheritance from a distant relative or a wealthy benefactor from overseas. They ask to pay a fee in advance to receive the inheritance.
-
Messages asking for donations to help the victims of the last humanitarian crisis that appeared in the news.
Spear phishing and whaling characteristics
This kind of phishing messages uses many of the generic phishing tricks in addition to social engineering techniques to convince the victim that he/she can trust the contents of the message.

To be more convincing, personal information about the victim is included in the message and they may even use hacked email accounts from friends, family members or co-workers. The message could talk about his/her hobbies, job, political affinity…
The collected private information can be used to blackmail the victim, identity theft, sabotage or it can be sold to the competitors.
Some examples of spear phishing or whaling :
-
A friend is stranded in another country and he/she is asking for some money to get home.
-
Message from IT asking to install a software update.
-
Message from a co-worker asking you to ignore the security protocols to get something.
-
Legal threats to the company, subpoenas or customer complaints.
Recommendations for all kinds of phishing
-
Don’t click on any link. In doubt, open a web browser independently and navigate to the web page using the Internet address of that service that you already had before receiving that message. Never use the Internet address included in the message.
-
Don’t reply to suspicious messages.
-
Don’t open any attached file.
-
Never make phone calls to the numbers included in the message.
-
Don’t provide any personal information.
-
If the message is suspicious, search part of the text or the subject in Internet. In many cases you’ll find it in many websites dedicated to talk about the last scams that appeared in Internet.
-
Be cautious and if it’s suspicious, confirm the information by other means or delete the message.
-
Report it to the authorities.
Keep reading about scam websites in the second part of this article.
Disclosure Statement: This site and BriskBard contains affiliate links, which means that I may receive a commision if you make a purchase using these links. As an eBay Partner, I earn from qualifying purchases.